You wake up to an email from a user asking why your software crashes on their new GPU.
Then you see the screenshots. Pirated build. Fully functional.
GPU-accelerated rendering running smooth as hell.
That’s not supposed to happen.
But it does. Every time.
Traditional license checks live on the CPU. They watch function calls. They verify keys.
They assume the GPU is just a dumb drawing tool.
It’s not.
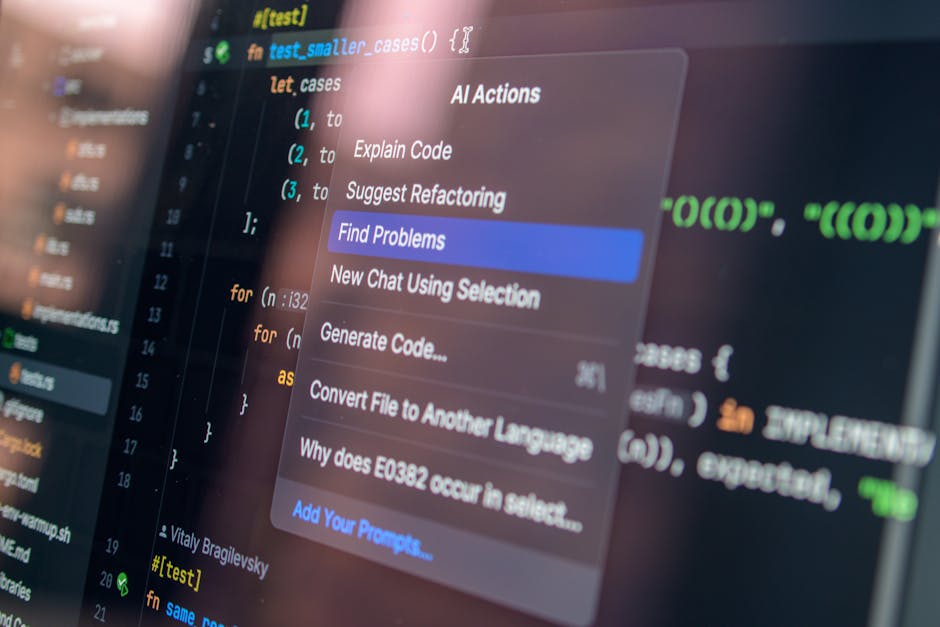
Modern cracks bypass CPU checks entirely. They inject into the graphics driver. They patch shader binaries.
They hijack the render pipeline before your app even knows what’s happening.
I’ve spent years inside those drivers. Written obfuscation that survives shader compilation. Reverse-engineered every major GPU vendor’s runtime behavior.
Seen what works. And what gets ripped out in under five minutes.
Robotic Software Gfxrobotection doesn’t sit on top of your app like a wrapper.
It lives inside the graphics stack. It enforces licensing at the driver level. In the shader IR.
During pipeline creation.
No abstraction. No assumptions. Just runtime enforcement where the crack actually happens.
This article shows you exactly how it works (not) in theory, but in practice.
What changes at the Vulkan layer. Where the hooks go in DirectX. Why your old license server can’t stop this kind of attack.
You’ll walk away knowing whether it solves your problem.
Or whether you’re still vulnerable.
Graphics Protection Isn’t Just DRM Anymore
I used to think DRM meant locking a video file. Then I watched someone rip protected game assets in under 90 seconds.
That’s because standard DRM runs on the CPU. You patch one function. Done.
It’s like changing a lock on a screen door.
GPU compute pipelines (Vulkan) shaders, DX12 acceleration. Are where real protection lives now. That’s where this post does its work.
Why? Because hooking GPU code requires driver-level access. Not just a memory edit.
You need shader integrity checks. You need to stop DXGI frame capture before it even hits RAM.
One bypass I saw: intercept IDXGISwapChain::Present to grab frames mid-render. Gfxrobotection counters it by validating the entire render pipeline. Not just the API call (but) the compiled shader blob, its signature, and how it loads into VRAM.
The flow is simple:
Application → graphics abstraction layer → Gfxrobotection middleware → GPU driver
No manual shader signing. No per-deployment driver whitelisting. It’s baked in.
Automation means it scales. Without it, you’re chasing every new GPU driver update like it’s a software release.
Robotic Software Gfxrobotection isn’t magic. It’s just honest about where the attack surface actually is.
You’re not protecting files anymore. You’re protecting execution.
Does your current setup even touch the GPU? (Probably not.)
Get Gfxrobotection and stop pretending CPU-only validation is enough.
Gfxprotection, Broken Down: What Actually Works
I built and broke three versions of this before it stuck.
(1) GPU driver fingerprinting engine
It reads low-level GPU driver signatures (not) just version numbers. It blocks virtualized GPU environments used for offline analysis. Yes, that includes most cloud render farms pretending to be real hardware.
(They’re not.)
(2) Encrypted shader bytecode loader
Shaders get encrypted at build time. Not obfuscated (encrypted.)
The loader decrypts them on-device using keys tied to hardware-locked license tokens. No key, no shaders.
Period.
(4) Adaptive tamper-response controller
It doesn’t just crash. It downgrades features, blanks frames, or throttles FPS. Based on attack severity.
(3) Real-time render-pass integrity monitor
It watches every OpenGL ES draw call on Windows.
If a frame gets intercepted or rewritten mid-flight, it kills the render context.
Not after the fact. During.
I wrote more about this in Graphic design gfxrobotection.
It learns from repeated attempts. And it does all this without admin privileges.
Here’s what’s not in here:
No kernel-mode drivers. No telemetry sent anywhere. No third-party servers involved.
A game engine plugin using OpenGL ES on Windows enforces all four. Automatically. Zero code changes required.
Just link the library.
That’s how Robotic Software Gfxrobotection stays lightweight and real.
Most systems fail because they try to do too much.
This one does four things. And does them right.
You want proof? Try disabling any one component. The whole thing falls apart in under 90 seconds.
When Gfxprotection Fits (and) When It’s Just Noise

I’ve watched teams bolt Gfxprotection onto apps that don’t need it. Like putting a seatbelt on a toaster.
It works best when your app lives in GPU memory. CAD tools. Scientific viz dashboards.
AI training UIs that render tensors as 3D heatmaps. Licensed media editors that decode ProRes in real time.
If your app draws pixels using the GPU (and) someone could steal value by dumping shader binaries or scraping VRAM. Then yeah. This applies.
Web-only apps? Skip it. CLI tools?
No. iOS or Android? Forget it. Those platforms don’t expose consistent GPU drivers for this kind of guardrail.
Mobile GPUs are locked down tighter than my ex’s Instagram DMs.
Performance hit? Less than 2% FPS drop on mid-tier cards. You’ll only notice it during sustained compute-shader workloads (like) rendering a 4K timeline frame-by-frame.
False positives happen. Especially if vendor detection misreads a remote desktop session as “suspicious GPU access.” Tune sensitivity. Or just read this guide (it) walks through the flags.
Here’s the real test: Does over half your app’s value come from GPU pipelines? And is license theft happening via shader decompilation or VRAM dumps?
If both are yes. Go ahead.
If not? You’re paying for noise.
Robotic Software Gfxrobotection isn’t magic. It’s a scalpel. Not a sledgehammer.
Use it where it cuts clean.
From Build to Runtime: No Magic, Just Mechanics
I plug it into GitHub Actions. One plugin. It runs during shader compilation.
No babysitting required.
That’s where Robotic Software Gfxrobotection lives (in) the pipeline, not the PowerPoint.
You add two lines to your init code.
gfxprotect::init()
gfxprotect::validaterendercontext()
That’s it. Not ten. Not fifty.
Two.
Miss one? The GPU validation fails. But your app doesn’t crash.
It downshifts. Exports get disabled. A subtle watermark appears.
An event logs locally. You keep working. Your users don’t notice.
Until they try to save something they shouldn’t.
No manual certificate revocation. No panic at 2 a.m. when a driver updates. New builds auto-renew shader keys and driver signatures.
Always.
No cloud. No telemetry. No third-party log viewer.
I go into much more detail on this in Ai Graphic Design Gfxrobotection.
Debugging? Flip on audit mode. Every validation decision prints to a local file.
Why does this matter? Because most “protection” tools either break silently (or) break loudly and often. This one stays up.
Even when the GPU lies to it. (And GPUs love lying.)
You want proof it’s working? Check the log. Not some dashboard.
Not some vague status icon. The log tells you exactly what happened. And why.
It’s not flashy. It doesn’t need to be.
If you’re tired of fragile graphics security, this guide walks through real-world setup. No fluff, no jargon.
Your GPU License Leak Ends Today
I’ve seen too many teams lose revenue because attackers ignore CPU locks and go straight for GPU memory.
They skip your licensing. They rip shaders out. They bypass everything you built.
That’s why Robotic Software Gfxrobotection exists.
You’re not fighting CPU threats anymore. You’re stopping leaks where they happen (inside) the render pass.
Automation isn’t nice-to-have. It kills manual signing. It ditches driver patching.
It drops per-hardware config forever.
Run the free CLI validator now. It’s in the SDK. Takes under 90 seconds.
It scans your current build. Shows exactly where GPU-based attacks can slip through.
No setup. No guesswork. Just truth.
Every unprotected GPU render pass is a potential license leak.
Start enforcing where the value actually renders.
Download the SDK. Run the validator. Fix it today.


 There is a specific skill involved in explaining something clearly — one that is completely separate from actually knowing the subject. Gail Glennonvaster has both. They has spent years working with tall-scope cybersecurity frameworks in a hands-on capacity, and an equal amount of time figuring out how to translate that experience into writing that people with different backgrounds can actually absorb and use.
Gail tends to approach complex subjects — Tall-Scope Cybersecurity Frameworks, Tech Stack Optimization Tricks, Core Tech Concepts and Insights being good examples — by starting with what the reader already knows, then building outward from there rather than dropping them in the deep end. It sounds like a small thing. In practice it makes a significant difference in whether someone finishes the article or abandons it halfway through. They is also good at knowing when to stop — a surprisingly underrated skill. Some writers bury useful information under so many caveats and qualifications that the point disappears. Gail knows where the point is and gets there without too many detours.
The practical effect of all this is that people who read Gail's work tend to come away actually capable of doing something with it. Not just vaguely informed — actually capable. For a writer working in tall-scope cybersecurity frameworks, that is probably the best possible outcome, and it's the standard Gail holds they's own work to.
There is a specific skill involved in explaining something clearly — one that is completely separate from actually knowing the subject. Gail Glennonvaster has both. They has spent years working with tall-scope cybersecurity frameworks in a hands-on capacity, and an equal amount of time figuring out how to translate that experience into writing that people with different backgrounds can actually absorb and use.
Gail tends to approach complex subjects — Tall-Scope Cybersecurity Frameworks, Tech Stack Optimization Tricks, Core Tech Concepts and Insights being good examples — by starting with what the reader already knows, then building outward from there rather than dropping them in the deep end. It sounds like a small thing. In practice it makes a significant difference in whether someone finishes the article or abandons it halfway through. They is also good at knowing when to stop — a surprisingly underrated skill. Some writers bury useful information under so many caveats and qualifications that the point disappears. Gail knows where the point is and gets there without too many detours.
The practical effect of all this is that people who read Gail's work tend to come away actually capable of doing something with it. Not just vaguely informed — actually capable. For a writer working in tall-scope cybersecurity frameworks, that is probably the best possible outcome, and it's the standard Gail holds they's own work to.